Introduction
If you’ve ever wondered how businesses keep their applications safe from hackers, data leaks, and malicious attacks, then you’ve already stepped into the world of preventing common security vulnerabilities in custom software. Security is no longer optional—it’s the foundation of trust, compliance, and long-term scalability.
With cyberattacks becoming more advanced and frequent, businesses must embed security into their development lifecycle rather than treating it as an afterthought. In this article, we’ll break down the vulnerabilities that most software teams overlook and explore practical ways to secure your custom applications from day one.
Need personalized guidance? Book a consultation:
https://appt.link/meet-with-chetan-chitriv-0E0czwAl/web-conference
What It Means: Understanding Common Software Security Risks
Security vulnerabilities are weaknesses in an application that allow attackers to exploit, manipulate, or extract sensitive data. In custom software development, these vulnerabilities often emerge from rushed deployments, poor coding practices, or missing validation layers.
Common Vulnerability Types
- SQL Injection due to unsanitized inputs
- Cross-Site Scripting (XSS) from improper output handling
- Broken Authentication leading to unauthorized access
- Insecure APIs exposing backend operations
- Misconfigured servers that leak sensitive data
By understanding these vulnerabilities early, teams can engineer safer systems that maintain integrity, confidentiality, and availability—even under attack.
Why It Matters: The Cost of Insecure Software
Security isn’t just a technical issue—it’s a business-critical factor that influences customer trust, compliance, and financial stability. Even a small vulnerability can lead to system outages, regulatory penalties, or severe reputation damage.
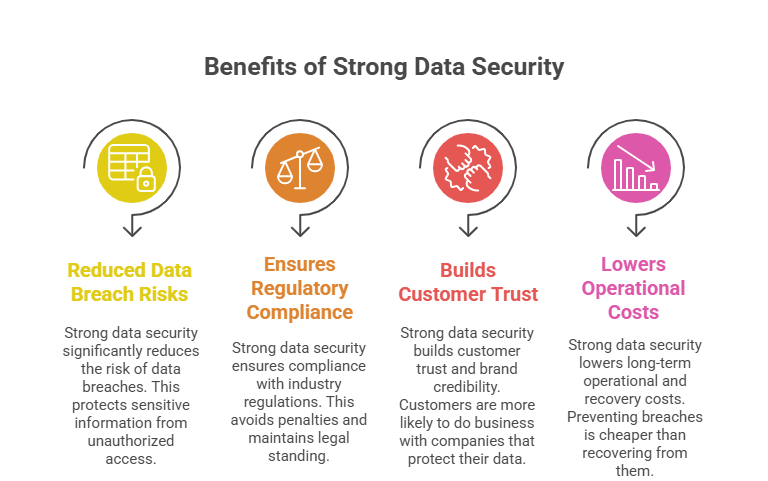
Why Preventing Vulnerabilities is Essential
- Reduces data breach risks significantly
- Ensures compliance with industry regulations
- Builds customer trust and brand credibility
- Lowers long-term operational and recovery costs
When security is built into the software lifecycle, businesses achieve a stronger, more resilient foundation that supports long-term innovation.
Step-by-Step Guide: Securing Your Custom Software
Step 1: Conduct a Thorough Risk Assessment
Identify potential entry points, weak spots, and system exposures early in development.
Step 2: Implement Secure Coding Practices
Follow industry standards like OWASP to prevent common vulnerabilities from creeping into your codebase.
Step 3: Use Strong Authentication & Access Controls
Apply MFA, role-based permissions, and secure session management to protect user accounts.
Step 4: Encrypt Sensitive Data
Ensure data is encrypted both in transit and at rest to prevent unauthorized access.
Step 5: Perform Regular Security Testing
Use penetration testing, automated scans, and code reviews as part of your continuous delivery process.
How Talentrise Technokrate Can Help
Talentrise Technokrate specializes in building secure, scalable, and compliant custom software solutions with security embedded at every layer. Their engineering processes follow strict standards designed to minimize vulnerabilities while enhancing performance.
What Talentrise Brings
- Secure-by-design development practices
- OWASP-driven coding frameworks
- API security, IAM, and data protection strategies
- Automated vulnerability scans and penetration testing
- Long-term maintenance with continuous security updates
With Talentrise, businesses get peace of mind knowing their applications are protected from evolving digital threats.
FAQ
1. What’s the most common vulnerability in custom software?
SQL injection and insecure authentication remain among the most frequent issues found in custom applications.
2. How often should security testing be done?
Ideally, during every major development phase—plus periodic penetration testing after deployment.
3. Can older applications be secured?
Yes. Through modernization, patching, refactoring, and adding new security layers, legacy apps can be brought up to today’s standards.
Conclusion
Preventing common security vulnerabilities in custom software is essential for protecting your organization from cyber risks and ensuring regulatory compliance. With the right strategies and an experienced partner like Talentrise Technokrate, businesses can build software that’s not only functional—but also secure, resilient, and future-ready.
Book a consultation:
https://appt.link/meet-with-chetan-chitriv-0E0czwAl/web-conference
Recommended Sites
- https://avestantechnologies.com/
- https://www.talentrisetechnokrate.com/
- https://technokrate.com/
- https://www.softwavetechify.com/
- https://chetanchitriv.in/
Here—check this out (Internal Reading):
Learn more about the Role of Low Code Platforms in Custom Software Development






