Introduction
In a world where digital threats grow more sophisticated every day, preventing common security vulnerabilities in custom software has become essential for businesses of all sizes. Whether you’re building a simple portal or a mission-critical enterprise application, your software must be engineered to withstand attacks, secure sensitive information, and maintain trust with users. Security isn’t just a technical requirement anymore—it’s a strategic asset that protects your brand, revenue, and reputation.
In this article, we explore the most common vulnerabilities, why they occur, and how you can safeguard your custom applications from day one. If you’d like expert help strengthening your systems, you can book a consultation here:
https://appt.link/meet-with-chetan-chitriv-0E0czwAl/web-conference
What It Means: Understanding Software Security Weaknesses
Security vulnerabilities are flaws in an application that attackers exploit to gain unauthorized access, steal data, or disrupt operations. These issues often arise due to poor coding practices, unvalidated inputs, outdated libraries, or misconfigurations.
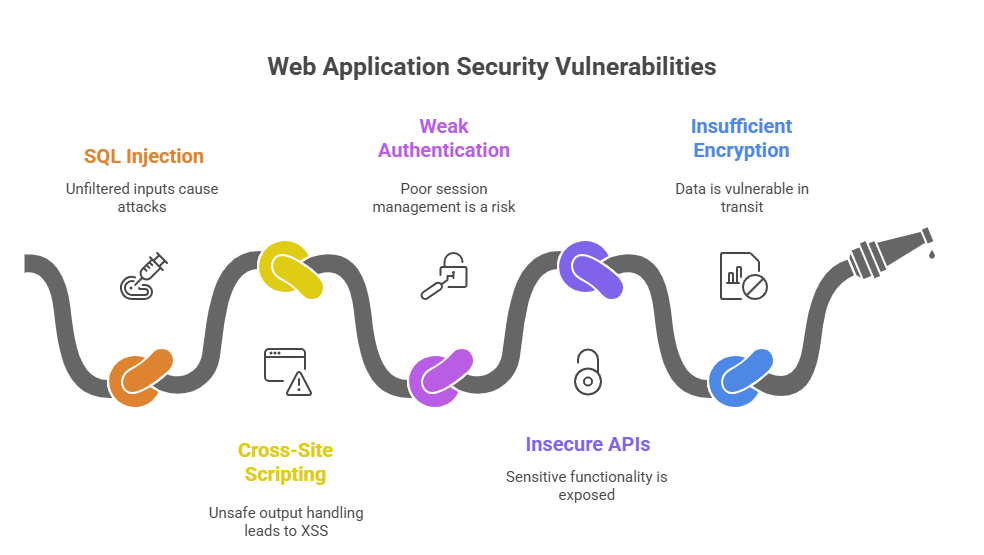
Common Security Weaknesses
- SQL injection attacks caused by unfiltered inputs
- Cross-site scripting (XSS) from unsafe output handling
- Weak authentication and session management
- Insecure APIs exposing sensitive functionality
- Insufficient encryption of data in transit or at rest
By identifying vulnerabilities early, teams can design stronger systems that minimize exposure and reduce risk during and after deployment. Strengthening the fundamentals helps businesses avoid costly breaches and maintain long-term reliability.
Why It Matters: The Impact of Poor Security
Security failures don’t just lead to data loss—they trigger downtime, legal consequences, financial penalties, and irreversible brand damage. With customers expecting seamless, secure digital experiences, application security directly influences business credibility.
Why Preventing Vulnerabilities Is Crucial
- Reduces the likelihood of cyberattacks and data breaches
- Ensures compliance with industry standards and government regulations
- Protects customer trust and strengthens brand reputation
- Lowers remediation costs and operational disruptions
When security becomes a core part of your development lifecycle, your software is better equipped to adapt, scale, and perform reliably—even in challenging environments.
Step-by-Step Guide: Securing Custom Software Effectively
Step 1: Perform a Security Risk Assessment
Identify potential threats, weak points, and system exposures before writing or modifying code.
Step 2: Adopt Secure Coding Standards
Use OWASP guidelines and industry frameworks to ensure vulnerabilities are avoided at the development stage.
Step 3: Strengthen Authentication & Authorization
Implement MFA, RBAC permissions, and secure token/session management.
Step 4: Encrypt Sensitive Data
Protect data both in transit and at rest using modern encryption algorithms.
Step 5: Continuously Test and Monitor
Conduct regular penetration tests, code audits, and automated vulnerability scans to catch issues early.
How Talentrise Technokrate Can Help
Talentrise Technokrate specializes in building secure, high-performance custom software with industry-grade protection. Their approach blends advanced security engineering with continuous monitoring to ensure every application is safe, stable, and compliant.
Why Businesses Trust Talentrise
- Secure-by-design development architecture
- OWASP-based coding practices and code review frameworks
- API security, IAM, encryption, and secure integrations
- Automated scanning, penetration testing, and patching
- Long-term maintenance to handle evolving threat patterns
With Talentrise, organizations gain tailored, future-ready software solutions that keep security at the core of every development decision.
FAQ
1. What is the biggest cause of vulnerabilities in custom software?
Most vulnerabilities arise from unvalidated input, poor coding practices, or outdated dependencies.
2. How often should vulnerability testing be done?
Testing should occur during every major development phase and at regular intervals after deployment.
3. Can legacy systems be secured effectively?
Yes—through patching, code hardening, encryption, and modernization, older systems can meet modern security standards.
Conclusion
Preventing common security vulnerabilities in custom software isn’t optional—it’s mission critical. Secure coding, systematic testing, and the right technology partner can help businesses stay protected against evolving cyber threats. With Talentrise Technokrate, organizations gain a trusted team focused on delivering secure, scalable, and robust digital solutions.
Book a consultation to strengthen your software’s security:
https://appt.link/meet-with-chetan-chitriv-0E0czwAl/web-conference
Recommended Sites
- https://avestantechnologies.com/
- https://www.talentrisetechnokrate.com/
- https://technokrate.com/
- https://www.softwavetechify.com/
- https://chetanchitriv.in/





